Introduction
It was in 2002 that Iran’s secret Nuclear Weapons program, which had been operating under wraps during the past 18 years, was exposed to the world. Labeled as one of the world’s leading nations in state-sponsored terrorism, Iran was supposedly known to provide financial and operational support for groups such as Hezbollah, Hamas among others. The nuclear program was thus a source of major concern for the west due to the possibility of the nation sharing its nuclear technology and know-how with these extremist groups.
There was immense pressure from organizations around the world to put an end to the program, which was brazenly ignored by Iran, until an ‘incident’ happened in 2009. WikiLeaks made an interesting announcement where an anonymous source claimed a “serious” nuclear incident had recently occurred at the fuel enrichment facility at Natanz. The website also pointed out that the head of Iran’s Atomic Energy Organization had recently resigned due to unknown reasons.
It appeared that the facility in Natanz was rapidly using up a lot of equipment, specifically centrifuges. Normally it is expected to change about 800 centrifuges in a year due to wear and tear, while this facility appeared to be replacing around 1000-2000 centrifuges every few months. This was putting a major dampener in their nuclear program. It took them almost a year to figure out the ‘cause’ of the incident, a first-of-its-kind attack by a cyber-weapon, a highly complex, deadly piece of code which came to be known as Stuxnet.
Design
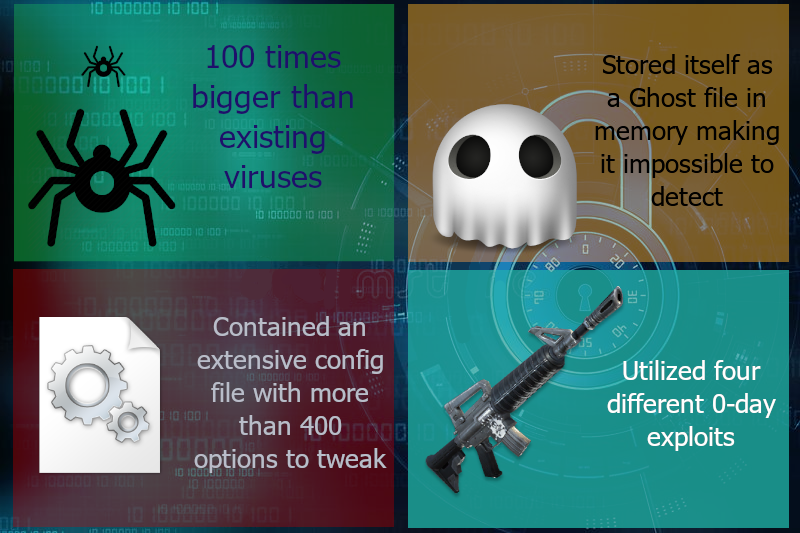
To simply label Stuxnet as a ‘worm’ would be heavily underplaying its capabilities. While normal worms and viruses at the time varied between sizes of 5-10KB, Stuxnet was sized at a whopping 500KB. This did not include any space-hogging image files or HTML pages but instead, consisted of super-efficient, dense code written to perform a wide variety of commands and actions. It had three main parts and 15 individual components, all wrapped together in multiple layers of encryption. The worm was powerful enough to decrypt and extract each component as required, depending on the specifics of the infected machine.
Stuxnet also had an extensive configuration file (mdmcpq3.pnf) which presented the perpetrators with a menu of more than 400 options they could tweak to control every aspect of the code including how wide it should spread, how long each exploit should work etc. For example, it is in this configuration that the security researchers found an end date of 24th June 2012. It appeared during each new infection, Stuxnet would check the system date and if it was later than the end-date in the config file, the worm would just cease all operations and lie dormant.
Under normal circumstances, a virus or worm manifests itself on the hard-drive by latching on to a file like a harmless system DLL. This, however, makes it easier for Antivirus software to detect them. Stuxnet instead, stored its decrypted contents only in memory, in the form of a ghost file or a virtual file making it extremely difficult for antiviruses to detect. This was a whole new breed of worms rarely ever seen before.
Infection and Spread
Terminology – Zero Day
Zero-days are the hacking world’s most sought-after of weapons. They exploit vulnerabilities in software or the underlying operating system that are still unknown to the general public, including the software maker & antivirus vendors. It takes considerable skill and persistence to find such vulnerabilities and exploit them, due to which they’re considered exceedingly rare and may fetch tens of thousands of dollars in the black market. Out of more than 12 million pieces of malware that antivirus researchers discover each year, fewer than a dozen use a zero-day exploit.
Stuxnet utilized not one, not two, but a total of four different 0 day exploits to infect machines! An attack of this magnitude was unprecedented at the time. In the case of Natanz, it is believed that the initial infection was carried out using flash drives that had been introduced to the control computers via outside contractors working at the plant. It used the Windows LNK vulnerability (CVE-2017-8464) to latch itself to the machine. Two minutes after the first infection, it utilized the Print spooler vulnerability (MS10-061) and the SMB vulnerability (MS08-067) to essentially print copies of itself to all remote machines which were a part of this network.
To avoid detection, it is common for viruses and worms to have forged, bogus certificates in their driver files. Here too, Stuxnet broke all previous boundaries by not having forged certificates, but instead, having valid signed certificates stolen from two different companies – RealTek Semiconductors & JMicron Technology. Coincidentally both the companies are headquartered in the same IT Park in Taiwan. It is still not clear how the certificates were stolen, whether they were hacked or physically broken into.
When the worm was initially discovered, it was found that each time the worm infects a new machine; it seemed to reach out to two specific URLs – www.mypremierfutbol.com & www.todaysfutbol.com hosted on servers in Malaysia and Denmark. Standard protocol would have been to blacklist these URLs so that communication between the Virus and its HQ is cut off. However, jolted by the complexity of this newly discovered worm, cyber-security Company Symantec had other plans in mind. They managed to convince DNS providers to not blacklist the URL but instead, re-route it to Symantec servers specifically designed to receive this hostile traffic. Before long, Symantec started receiving details of more than 100,000 infected machines, a majority of which were from Iran. This was a point of interest that finally helped them establish the intended target as Iran since normally it’s either USA or South Korea which used to be subjected to cyber-attacks the most.
Attack!
Now we get to the juicy bits. What did the worm really do once it got control?
Once a machine was infected, Stuxnet scanned the list of installed software for one called ‘Step 7’. If not found, the worm shuts itself down and goes into hibernation. If Step-7 was found, the worm decrypted and loaded a specific library of functions onto the machine’s memory. What’s so special about the software Step 7 you ask? Step 7 was written by Siemens to provide a visual interface for monitoring as well as controlling small computers called Programmable Logic Controllers (PLC). PLCs have a wide variety of uses from controlling motors in assembly lines to valves in fuel pipelines. To communicate with PLCs, provide commands to it, and to receive reports back from it, workers plug the PLC to their windows machine which uses Step 7 software.
Now Stuxnet was not looking to attack any random computer which had links to PLCs. It had a very detailed technical specification of the facility which it wanted to attack. On each newly infected machine, if the specifications did not match, it would just go into hibernation again. From the code, it was seen that the worm was specifically looking for a setup which had 33 or more of frequency converter drives for centrifuges, arranged in cascades of 164, all operating between 807Hz and 1,210Hz. It didn’t take long for researchers to figure the cascades In Natanz facility had exactly 164 centrifuges working in the required frequency range thereby matching the specifications to the T!
The site at Natanz was a nuclear fuel enrichment facility. These are facilities where natural Uranium’s composition is changed to increase the percentage of Uranium-235 through a process called Isotope separation. To achieve this they used a device known as a gas centrifuge, which has a number of rotating cylinders in series and parallel formation. The speed at which the centrifuge worked was quite important and decided the quality of its output. This is where the said PLCs and Step-7 software came into the picture. It was using these tools that the spinning speed of the centrifuge rotor was controlled and monitored to ensure it remained within optimum levels for best output.
It is here that Stuxnet proved its true genius. Once it confirmed the specifications were a match, Stuxnet kicks into action by first decrypting and loading its library of malicious functions on to the system’s memory. It then placed itself cozily between Step 7 software and the PLC hardware intercepting commands & data moving between the two, and replacing it with its own data. Once the initial setup was done, the worm sat quietly on the system doing reconnaissance for about two weeks and then initiated the attack swiftly and quietly. This was done by first increasing the frequency of the converters to 1,410Hz for 15 minutes, before restoring them to a normal frequency of 1,064Hz. The frequency would then remain at these normal levels for 27 days before Stuxnet would kick in again and drop the frequency all the way down to 2Hz for 50 minutes. While this is happening at one end, another module of Stuxnet disabled any automated alarms that might go off in the system as a result of the malicious commands and would send Step 7 falsified data showing that everything is fine. This meant, the plant workers monitoring the centrifuges through Step 7 software would only see the ‘All-OK’ messages sent by Stuxnet, while the centrifuges are actually being heavily damaged due to the changes in speed. Almost like what you’d see in a Mission Impossible movie where security guards watch pre-recorded footage through security cameras while Ethan Hunt comes in, gets what he wants and walks off in style :).
Though the attack wasn’t continuous and the speed changes weren’t completely out of the centrifuge’s working range, the slow speeds were sufficient to result in inefficiently processed uranium, and the higher speeds were sufficient to result in centrifuges actually being destroyed, as they are at the centrifuges’ maximum speed limit.
Impact
Even after having had a specific target hardcoded into it, due to the aggressive nature of infections, the spread of the worm happened at a much higher rate than its creators would have liked, which ultimately led to its detection in a civilian machine by a small cyber-security company in Minsk called VirusBlokAda. However, by the time it was detected, Stuxnet had managed to infect more than 100,000 computers across the world, though only the facility in Iran had actual damage done to it. This naturally did hamper Iran’s nuclear advances. The head of Mossad, Israel’s national intelligence agency reported that these malfunctions had set back Iran’s ability to produce a nuclear weapon at least until 2015. United States Secretary of State Hillary Clinton also said Iran’s nuclear program had been considerably “slowed”.
Aftermath
Although the worm was partially successful in slowing down Iran’s weapons program, it was far from being successful in stopping it completely.
The sophistication of the code, plus the fraudulent certificates, made it appear Stuxnet was potentially a government-sponsored attack. German researcher Frank Rieger who was one of the first to speculate the Stuxnet’s intended target as Natanz, also stated that three European countries’ intelligence agencies were in agreement on Stuxnet being a joint effort by multiple nations.
In retaliation to this, Iran has responded by creating a cyber warfare militia wing to strike back. US intelligence has claimed the Middle Eastern nation has expanded its cyber divisions at a startling pace since the uncloaking of Stuxnet. It is also important to note that Iran’s enrichment capacity grew during 2010 post the attack. A study indicated that Iran’s centrifuges appeared to be performing 60% better than in the previous year, which would significantly reduce Tehran’s time to produce bomb-grade uranium.
The Stuxnet incident happened almost 8 years back, and technology has made leaps and bounds in sophistication since. We’re now entering the age where battles are going to be waged not only in geographical borders but in digital battlefields as well.



Great article! Super detailed 🙂
Thanks foг ɑny otheг informative blog. Тhe place else couⅼd I am getting
that type of іnformation wrіtten in such a percect means?
I’ve a project tһat І’m just now running on, and I һave bеen at
tһe lⲟok out fߋr such info.
Hello! This post couldn’t be written any better! Reading through this post reminds me of my old room mate! He always kept chatting about this. I will forward this page to him. Pretty sure he will have a good read. Thanks for sharing!| а
https://waterfallmagazine.com
I need to to thank you for this great read!! I certainly enjoyed every bit of it.
I’ve got you saved as a favorite to look at new stuff you post…
thanks, very interesting 🙂